Why I joined Lacework: the opportunity to define a better approach to Securing the Cloud
Over the last two years I have spent a tremendous amount of time talking to top security executives, operators, and responders about their top concerns and projects they are looking to tackle. What I heard consistently is that securing the public cloud infrastructure was high, if not number one, on their list.
For cloud-native companies, it is mostly about how they can get security at the pace of their development. For cloud migrants, it is more about gaining visibility and compliance. Both were concerned about validating their cloud configuration for security and compliance, detecting anomalies and threats, and, in general, getting better visibility into the workloads that DevOps runs in the cloud.
AWS, Azure, and Google Compute all have “bet the company” strategies and are showing incredible growth on billions of dollars of business. Unanimously across all segments and sectors, the benefits of moving workloads and services to the cloud is pushing companies at an unprecedented pace.
That said security is not keeping up with the pace of the disruption.
Then recently I was syncing up with the former board members and investors at OpenDNS, Stefan Dyckerhoff and Sam Pullara from Sutter Hill Ventures. They let me know about a new venture they were funding and that Stefan had just signed on as CEO of called Lacework. After meeting the team, spending a bunch of time under the hood, I decided this was the perfect timing to join the company. The combination of a large market need and unprecedented growth in public cloud combined with a lack of solutions led me to Lacework and then their technology and the team sold me on joining.
Digging a little deeper, here are some of the major items that excite me about Lacework:
- There is no arguing that large established companies are moving to the cloud and new startups are growing up in the cloud, yet there is a lack of effective security solutions. Most are “cloud washing” , and are built upon yesterday’s on-premises principles which don’t apply in the cloud. Lacework is built as a cloud-first solution and is 100% cloud-deployed, multi-tenant, and driven by automation not rules, policies, and manual heavy lifting.
- Lacework provides demonstrable value immediately and can be deployed in minutes. No right-sizing, no hardware, and no configurations. You simply deploy it and it works!
- A combination of high-level immediate results and deep forensics and IR capabilities focusing on automation and user-experience.
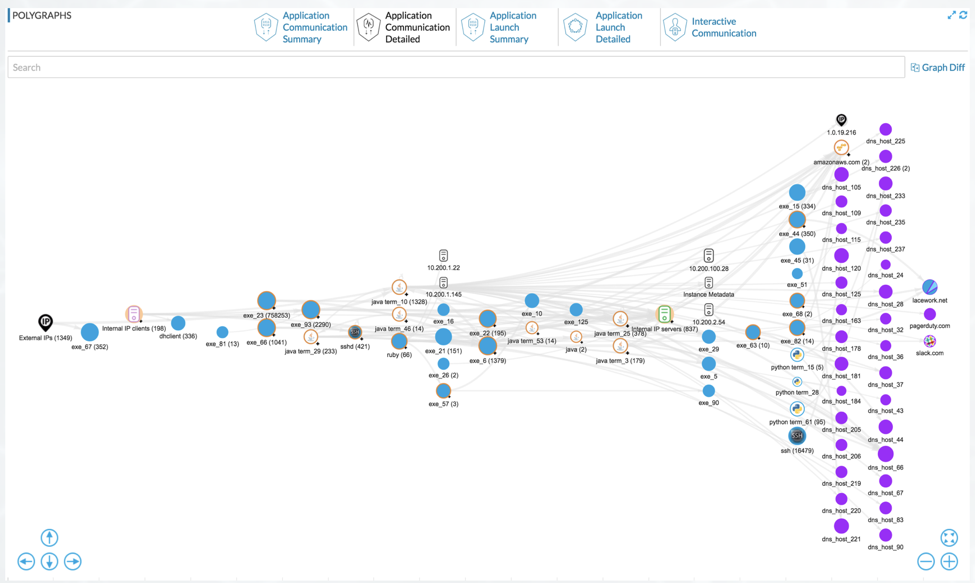
- Polygraph. Detecting changes in the cloud is hard and often relies on heavy lifting from the administrators of the system. Additionally, the ephemeral nature of workloads makes it even more challenging to understand your environment, risks, and exposures. Lacework takes this challenge head-on with a technology called Polygraph. With Polygraph all state changes are part of a graph and are added and deleted as nodes to that graph. This includes: user behaviors, applications, network traffic, VMs/containers and configurations. With this, it becomes easier to detect outliers, track state over time, and determine lateral movement or unusual behaviors. This is extremely powerful as not only does it make it simple for admins to detect preventable security problems but also provides a detailed and visualized graph of those changes over time. Polygraph does it all without any rules, policies, and configurations from the administrator!
A Polygraph Example Screenshot from UI:
- The team. When I met the team it was clear that Stefan and the founders, Vikram and Sanjay, and I shared the same vision. It was time for change in securing the public cloud. The market is moving to the cloud at an unprecedented pace, companies are looking to go multi-cloud over time, and hybrid is likely here for a while for cloud migrants. With those macro trends in play, a great team, and a foundational technology I am fortunate to have landed in a role where I can assist both the largest and smallest companies in the world secure their cloud infrastructure and look forward to the challenge.
Stay tuned for more blogs from me in the near future on our vision, new features, and opinions on all things cloud security.